In today's interconnected world, remote IoT (Internet of Things) devices play a crucial role in various industries, from healthcare to manufacturing. However, ensuring secure communication for these devices, especially when they are behind a firewall, is a significant challenge. RemoteIoT behind firewall examples provide practical insights into overcoming this hurdle while maintaining robust security measures.
As more businesses embrace IoT technology, the need for secure and efficient remote access to IoT devices becomes increasingly important. Firewalls act as a protective barrier, but they can also create barriers for remote IoT devices trying to communicate with external networks. Understanding how to configure and manage remote IoT devices behind a firewall is essential for maintaining both functionality and security.
This comprehensive guide explores the concept of remote IoT behind firewalls, offering practical examples and expert advice to help you implement secure and reliable solutions. Whether you're a network administrator, IT professional, or IoT enthusiast, this article will provide valuable insights to enhance your understanding and capabilities in this domain.
Read also:Shows Like Power Book 2
Table of Contents
- Introduction to RemoteIoT Behind Firewall
- Security Challenges with IoT Devices Behind Firewalls
- Network Architecture for RemoteIoT Behind Firewall
- Examples of RemoteIoT Behind Firewall Implementations
- Using VPN Solutions for Secure Connectivity
- Cloud-Based Solutions for RemoteIoT
- Firewall Configuration Best Practices
- Importance of Data Encryption in RemoteIoT
- Monitoring and Managing RemoteIoT Devices
- Future Trends in RemoteIoT Behind Firewall
- Conclusion
Introduction to RemoteIoT Behind Firewall
RemoteIoT refers to the ability to access and manage IoT devices from a remote location. When these devices are placed behind a firewall, ensuring secure and uninterrupted connectivity becomes critical. Firewalls are designed to protect internal networks from unauthorized access, but they can also block legitimate traffic from IoT devices. Understanding how to configure firewalls for remote IoT devices is essential for maintaining both security and functionality.
There are several methods to enable remote IoT communication behind a firewall, including port forwarding, reverse proxies, and secure tunneling. Each method has its own advantages and limitations, and choosing the right approach depends on the specific requirements of your network and devices.
Security Challenges with IoT Devices Behind Firewalls
Understanding Firewall Restrictions
Firewalls are a double-edged sword when it comes to IoT devices. While they provide a layer of protection against external threats, they can also hinder communication between IoT devices and external networks. Common challenges include:
- Blocking of outbound connections
- Restrictions on specific ports and protocols
- Limited visibility into IoT traffic
Securing IoT Data Transmission
Ensuring the security of data transmitted by IoT devices is paramount. Data breaches can have severe consequences, especially in industries such as healthcare and finance. Implementing strong authentication mechanisms and encryption protocols is essential to protect sensitive information.
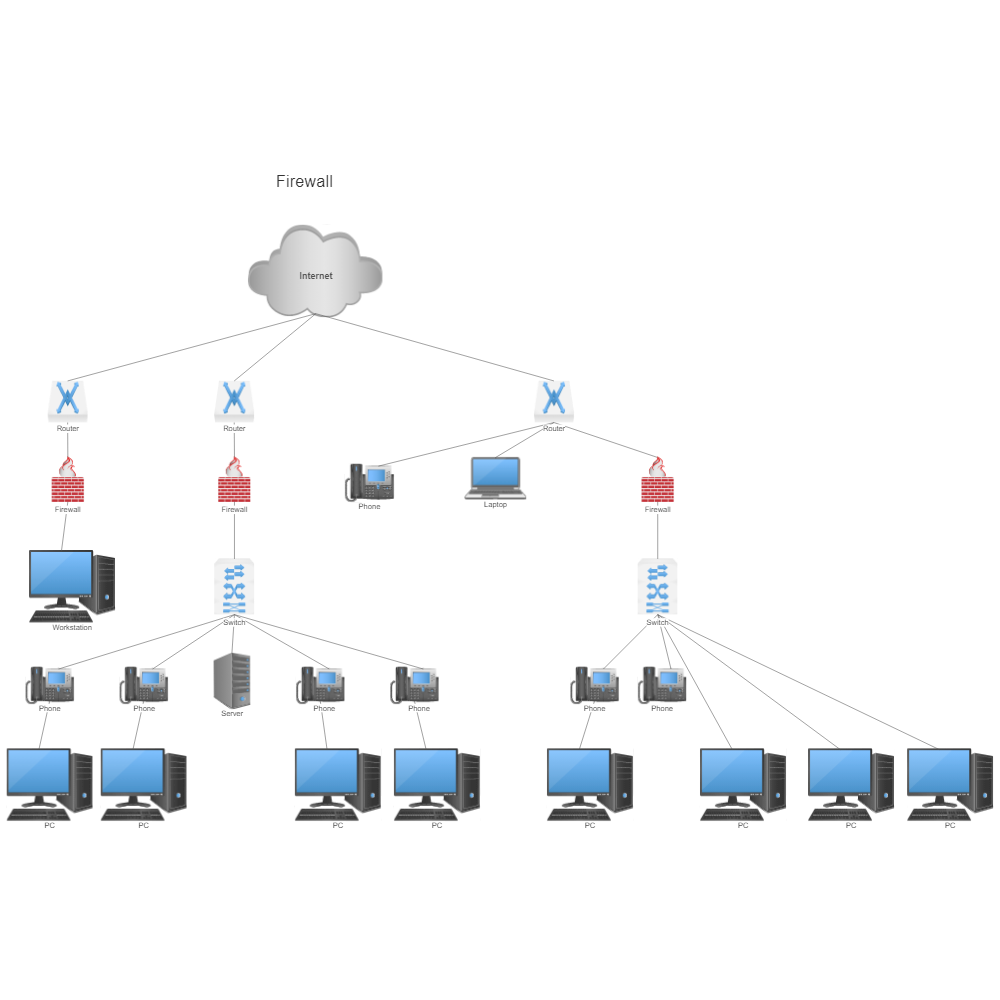
Network Architecture for RemoteIoT Behind Firewall
Designing an effective network architecture is key to enabling secure remote access to IoT devices behind a firewall. The architecture should include:
- A central gateway for managing IoT devices
- Secure communication channels using protocols like HTTPS or MQTT over TLS
- Firewall rules that allow only necessary traffic
By carefully planning the network architecture, organizations can minimize security risks while maximizing the functionality of their IoT devices.
Read also:Simple Behind The Ear Tattoos
Examples of RemoteIoT Behind Firewall Implementations
Example 1: Port Forwarding
Port forwarding is a common technique used to enable remote access to IoT devices behind a firewall. This method involves configuring the firewall to forward specific ports to the internal IP address of the IoT device. For example:
- Forward port 8080 to the IoT device's web interface
- Forward port 1883 for MQTT communication
Example 2: Reverse Proxy
A reverse proxy acts as an intermediary between external users and IoT devices. It can enhance security by hiding the internal network structure and providing an additional layer of authentication. Popular reverse proxy solutions include Nginx and Apache.
Using VPN Solutions for Secure Connectivity
Virtual Private Networks (VPNs) offer a secure way to access IoT devices behind a firewall. By creating an encrypted tunnel between the remote user and the internal network, VPNs ensure that all communication remains private and secure. Key considerations when implementing a VPN solution include:
- Selecting a reliable VPN provider
- Configuring firewall rules to allow VPN traffic
- Ensuring compatibility with IoT devices
Cloud-Based Solutions for RemoteIoT
Cloud platforms such as AWS IoT Core and Microsoft Azure IoT Hub provide robust solutions for managing remote IoT devices. These platforms offer features like device management, data analytics, and secure communication protocols. By leveraging cloud-based solutions, organizations can streamline their IoT operations while maintaining high levels of security.
Firewall Configuration Best Practices
Defining Clear Rules
Firewall rules should be carefully defined to allow only necessary traffic while blocking potential threats. Best practices include:
- Using whitelist rules to permit specific IP addresses
- Restricting access to specific ports and protocols
- Regularly reviewing and updating firewall rules
Monitoring Traffic
Continuous monitoring of network traffic is essential for identifying and mitigating potential security threats. Tools like Snort and Wireshark can help analyze traffic patterns and detect anomalies.
Importance of Data Encryption in RemoteIoT
Data encryption plays a crucial role in securing remote IoT communications. By encrypting data both in transit and at rest, organizations can protect sensitive information from unauthorized access. Common encryption protocols used in IoT include:
- TLS (Transport Layer Security)
- SSL (Secure Sockets Layer)
- AES (Advanced Encryption Standard)
Monitoring and Managing RemoteIoT Devices
Effective monitoring and management of remote IoT devices are essential for maintaining their performance and security. Tools like IoT dashboards and network monitoring software can help administrators track device status, analyze performance metrics, and respond to potential issues in real-time.
Future Trends in RemoteIoT Behind Firewall
The field of remote IoT behind firewalls is rapidly evolving, with new technologies and solutions emerging to address the challenges of secure connectivity. Key trends to watch include:
- Advancements in edge computing for improved performance
- Integration of AI and machine learning for enhanced security
- Development of new protocols specifically designed for IoT
Conclusion
RemoteIoT behind firewall examples provide valuable insights into enabling secure and efficient communication for IoT devices. By understanding the security challenges, implementing robust network architectures, and leveraging advanced technologies, organizations can unlock the full potential of their IoT ecosystems.
We invite you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more in-depth information on IoT and related topics. Together, let's build a safer and more connected future!
Data sources: Cisco, AWS, Microsoft Azure.